Rethinking authentication to be both continuous and seamless with cryptographic attestation.
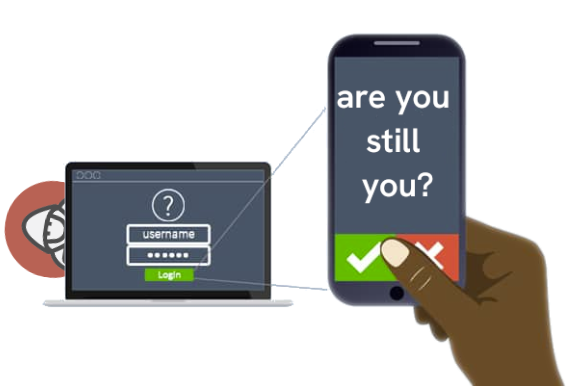
Let’s be real: Authentication is broken. Passwordless authentication or today’s use of multiple factors or biometrics can’t stop targeted attacks, the volume of which we have never seen before, not to mention the nature of these processes consistently interrupts end-users to reauthenticate throughout their workday.
The mismatch affects everyone: decision makers want tested and proven “zero-trust” authentication to thwart the barrage of attacks, while end-users crave frictionless security measures that help to eliminate the pressure and outsized responsibility that comes with protecting their organization from security threats.
These problems are fundamental. Authentication derives from an era where, after validating your credentials, we can trust that you remain you. But if you fall prey to a targeted spearphishing attack, hackers can lurk on your computer and impersonate you after the authentication step, thus thwarting this assumption. You aren’t just you, you are inadvertently harboring hackers and you’ve taken them past the security booth. This simple, ubiquitous attack pattern of impersonation is the secret behind why hackers have had such an easy time “owning” the world over the past two decades. I can say that with confidence because, before I turned from the dark side, I used to be one of them.
However, a new, super-charged form of continuous authentication offers a solution. The gist? If traditional authentication is bringing a single nail to a gunfight, cryptographically attested continuous authentication is a nail gun. This is a groundbreaking reimagining of what authentication could be, so bear with me while I explain!
Answered in this article:
- What does current authentication look like?
- What does the ideal authentication system look like?
- How did we rethink authentication?
- How does cybersecurity (and your industry) change with continuous authentication?
- How do we use this technology to build a more secure digital world?
Fact: Authentication has no clothes!
To get started, consider this fictional portrait of current authentication methods:
Bob does email catch-and-release for Bullzeye, the superstore chain whose brand name is particularly fitting for what is about to happen to our friend Bob here.
Every morning when Bob sits down in front of his computer to start his long day of tasks, he is prompted with traditional 2-step authentication that tells Bullzeye’s administrators that the person typing on Bob’s computer is, indeed, Bob. Of course, the purpose of authentication here is to ensure that Bob’s system hasn’t been overtaken by some nefarious, hooded hacker, who sees no issue with compromising valuable Bullzeye data or setting into motion a series of events leading to the total demise of Bullzeye’s systems.
According to security standards and industry best practices, Bullzeye has nothing to worry about, right? Bob inputted his name and security key and successfully authenticated himself. In fact, he was prompted to authenticate multiple times throughout his workday–so how could there possibly be a problem?
Well, a few days ago, Bob opened a spammy-looking email whose footer was painted with a big blue button: UNSUBSCRIBE. Bob is adamantly against a messy inbox, so he clicked the button. But what Bob didn’t know is that this email actually came from Alice—one of those nefariously hooded hackers—and next thing you know, his computer is infected with malware. Alice can issue commands on Bob’s computer as though she were him, completely undetected.
Bob got owned. Alice wins the day. Classic spearphishing.
We need a tailor! Reimagining authentication
Now, let’s show Alice’s lateral movement can be thwarted by continuous authentication.
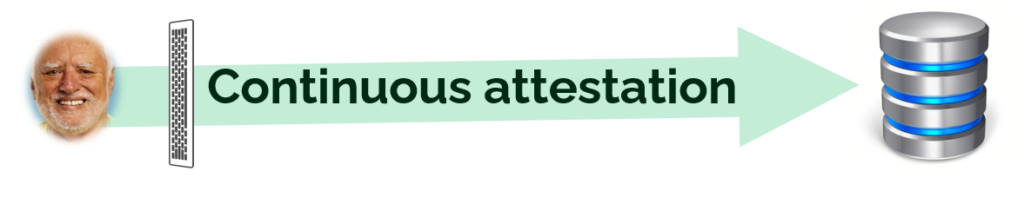
Bob takes the bait, and Alice is positioned to move laterally through Bullzeye’s network, lurking in the shadows. However, this time, Bullzeye is using a form of continuous authentication based on cryptographic signatures attributed to each of Bob’s keystrokes. For example, if Bob hits the “C” key, the server will automatically authenticate Bob as the author because his signature is verifiable by his public key. In other words, every keystroke attests that Bob is Bob, Bullzeye employee extraordinaire — or at least someone sitting physically on Bob’s desk after Bob authenticated.
So now we have Alice, poised to overtake more of Bullzeye’s network from Bob’s computer and credentials, but something isn’t working right. Her keystrokes to other services don’t have or match Bob’s signatures, throwing up a warning for Bullzeye’s high priests. Alice is stuck, unable to move in the shadows masquerading as Bob, fear and loathing struck firmly within her heart.
Throughout every workday, Bob’s keystrokes consistently attest that the Bullzeye employee, not the hacker, is in fact the individual issuing commands–all automatically. This is called cryptographic attestation. The kicker? The attestation was automatic, meaning that Bob is being continuously authenticated without anyone needing to constantly ask Bob for his credentials!
Cryptographic attestation is the future of continuous authentication
Here’s the gist: While traditional password and key 2FA/MFA and biometrics have made significant strides in improving security, they have glaring vulnerabilities. Frankly, these methods are fundamentally broken: they do not provide adequate security against today’s adversaries. If a hacker strikes someone’s workstation during an active 2FA/MFA session, the other endpoint cannot distinguish between legitimate and illegitimate commands since they are all being done in the name of the worker: Phishing, ransomware, supply chain attacks, and subsequent undetected lateral movement ensues. Game over.
Zero-trust continuous authentication based on a user’s individual keystrokes offers a unique solution to these shortcomings, especially when assigning every input with its own unique cryptographic signature.
Unlike authentication based on static credentials and biometrics—all too often stolen or imitated, and almost always wrought with inconvenient processes—continuous authentication equipped with cryptographic attestation provides a highly effective, dynamic, and frictionless method of security. This technology extends zero trust to include the endpoint, bringing an extra layer of security to contain hackers before they strike, safeguard employee workstations, and protect sensitive company data.
How to rethink continuous authentication
Let’s address the elephant in the room —
Having spent the better portion of my professional life in this field, I have never seen continuous authentication being executed at 100% of its potential. Nowhere close. But why?
Some studies show poor match rates and susceptibility to replay attacks, with other concerns pointed at the legitimacy of security and quality of usability. This is because continuous authentication is usually based in behavioral biometrics, which operate via assessment of a user’s typing behaviors to determine that the individual typing is actually Bob, not Alice.
“Behavioral biometrics” sounds like tomorrow’s fancy answer to cybersecurity’s biggest problems, but has proven itself to be a highly complex and opaque method of authentication, often wrought with troubling false negatives/positives resulting from cloudy user variation, inaccurate behavioral calibration, and other environmental factors. Natural variations in user behavior can impact the accuracy of the authentication process, requiring constant retraining or calibration, leading to potential inconvenience for users and decreased effectiveness of the system. If Bob returns to work Monday morning with a sprained hand, what happens when the authentication system is unable to detect his usual typing patterns and flags him as a threat?
Thwarting inconvenience in authentication
Above all, the result here is inconvenience, plaguing organizations to suffer severely stunted workflows every time a breach occurs. Behavioral biometrics might be “continuous,” but only under the conditions the technology itself sets. The moment one of these conditions is challenged, the seamlessness of the “continuous” factor quickly turns into an afternoon trying to make up for the work lost that morning while trying to get Bob back onto his computer.
So then, if continuous authentication based in behavioral biometrics are indeed the half-baked solution described above, a company decision maker might then choose to go with traditional password MFA. However, the outcome is still needlessly complicated: An employee’s phone app consistently harps on them to re-authenticate before resuming tasks, or perhaps a Yubikey that needs to be clicked on to authenticate every action. To add insult to injury, even if Bob follows this rather monotonous process, he can’t be sure of what they are authenticating–the requested authentication could easily be sent from a hacker acting as the company, who upon Bob’s authentication lets them directly into the system.
Next thing you know, Bob is shedding tears of shame and frustration all over again.
But with continuous authentication secured via cryptographic attestation, all of this complexity and shame gets thrown out. There is no need to assess the characteristics of every last employee’s typing behaviors; no need for ceaseless re-authentication requests between tasks; no need for holding the Bobs of the world responsible for an entire organization’s security. Cryptographically attesting Bob’s every keystroke—in real time, all automatically, without interrupting Bob’s workflow—is not only a more secure method of authentication, but promises a level of convenience that traditional MFA and biometrics leave out.
Leaving convenience out of security is essentially akin to throwing the baby out with the bathwater, resulting in a compromised and authentication-fatigued world. Let’s not!
Cryptographic attestation vitalizes continuous authentication
We have argued that biometric and multifactor authentication is fundamentally broken. But it’d be misleading to think about cryptographic attestation as a separate technology. Cryptographic attestation is multifactor authentication, with one essential difference. For Keystrike, the second factor is the keyboard, where every keystroke is continuously cryptographically attested. Where traditional MFA stops after two pieces of authenticating evidence have been presented, our approach is always attesting, authenticating, and warning system admins of potential attack—seamlessly, automatically.
Here is how the cybersecurity world changes with continuous cryptographic attestation:
1. Convenience: Automation, easy deployment, and malleable integration
With cryptographically attested keystrokes, there is no need for biometrics or assigning employees multiple multifactor sign-ins per day. The end-user’s keystrokes take care of authentication behind the scenes, providing the time and space employees need to build a healthy work environment.
Additionally, implementing continuous authentication based technology is relatively straightforward. It can be seamlessly integrated into existing authentication systems and customized to meet specific organizational requirements. The deployment process is user-friendly, requiring minimal to no training or disruption to the workforce.
2. Bolstering convenience by removing friction
Unlike traditional authentication methods that often interrupt the user’s workflow with repeated prompts or additional hardware requirements, continuous authentication with cryptographic attestation seamlessly operates in the background. Users authenticate themselves with every keystroke, reducing friction and enhancing productivity.
3. Eliminating user shame
A cyberattack can induce feelings of shame in the user who accidentally let the hacker in. As seen in the statistics above, these attacks can be extremely costly, leading to undue stress on higher-ups, stakeholders, and the company as a whole—an extremely guilt-ridden situation to be in if you’re the employee whose machine compromised the company.
Why are employees bearing the weight of their organization’s cybersecurity on their shoulders? Ponder that for a second. That’s right, it’s absurd!
Continuous authentication with cryptographic attestation effectively eliminates user shame by continuously confirming that the individual typing is who they say they are. This method of authentication eliminates passwords altogether, reducing the risk of human error and eliminating the shame associated with password-related mishaps.
Of course, while this technology can be helpful, organizations should always teach and encourage cybercrime awareness and implement best practices. Be wary of phishing, spearphishing, ransomware, and the other attack vectors listed here. Employees and end-users of all circumstances should stay educated on what to do should they suspect the system has been compromised.
Building future-forward cybersecurity practices: For SaaS, for web, for everyone
Continuous, cryptographically attested authentication has the potential to make a significant impact across various industries. In sectors such as finance and banking, cryptographic attestation could enhance transaction security, safeguarding sensitive financial information, and reducing the risk of fraud. How? By providing secure remote access even when the endpoint is compromised. In healthcare, it could strengthen patient data protection, ensuring that only authorized individuals can access confidential medical records. It could also revolutionize supply chain management, enabling verifiable authentication and tracking of goods, reducing counterfeiting risks, and ensuring product integrity.
Industries such as government, defense, and critical infrastructure could benefit from the enhanced security and accountability provided by cryptographic attestation, protecting against unauthorized access and ensuring the integrity of sensitive systems. With its ability to provide verifiable proof of authentication, continuous cryptographic attestation holds the potential to transform security practices across a wide range of industries, leading to increased trust, efficiency, and resilience in our digital ecosystems.
But here is the most important factor for the future: Bob never has to worry about Alice again. With every keystroke, the end-user, the employee, is secure. And Alice?—Alice is trapped, her lateral movement thwarted.